TL;DR Summary:
URL Exploit Exposed: Attackers used simple capitalization tricks in Google's removal tool to deindex live pages from search results.Massive Website Damage: Hundreds of sites suffered repeated removals, forcing owners into endless restoration battles.Key Protection Lessons: Implement monitoring alerts, consistent URLs, and rapid response plans to safeguard visibility.How a Simple URL Exploit Let Attackers Remove Pages from Google Search
A critical vulnerability in Google’s “Remove Outdated Content” tool exposed a significant security flaw that allowed malicious actors to deindex live web pages from search results through a surprisingly simple URL manipulation technique. The exploit, which impacted hundreds of legitimate websites before being patched, demonstrates how even minor technical oversights can have major consequences for online visibility.
Understanding the URL Capitalization Vulnerability
The core issue centered around how Google’s tool processed URL capitalization compared to web servers. While servers typically treat example.com/Page and example.com/page as distinct URLs, Google’s removal system failed to properly account for these case sensitivity differences.
Attackers exploited this discrepancy by submitting removal requests using incorrect URL capitalization that would trigger a 404 error. The system would then erroneously remove the legitimate, correctly-capitalized page from Google’s index, effectively making it invisible in search results.
How the Exploit Impacted Website Owners
The attack pattern was deceptively straightforward but created significant disruption. Bad actors would flag pages as outdated by referencing content no longer present on the current version. While these claims were false, they successfully manipulated the tool’s intended purpose of removing genuinely outdated or inaccessible content.
Site owners found themselves caught in an exhausting cycle of monitoring and restoration. Even after reinstating pages through Google Search Console, repeated removal requests would trigger new deindexing – creating a frustrating game of digital whack-a-mole.
Real-World Cases Reveal Broader Implications
The vulnerability’s impact extended beyond theory into concrete examples of reputation management abuse. In one notable case, a journalist who had previously faced legal pressure from a tech CEO over unfavorable coverage saw their vindicated article repeatedly vanish from search results through this exploit.
This particular incident highlighted not just the technical flaw, but also raised questions about response times and accountability. The vulnerability reportedly existed for nearly two years before being addressed, despite its potential for abuse in suppressing legitimate content.
Technical SEO Lessons from the Incident
The episode offers several key insights for managing search visibility and technical SEO:
- URL case sensitivity remains a crucial technical consideration that can impact indexing
- Public-facing content management tools require robust validation against spoofing
- Consistent URL formatting and canonical implementations help reduce vulnerability
- Regular monitoring of search console data is essential for catching unusual indexing patterns
- Quick response procedures for suspicious deindexing need to be established
Search Visibility Protection Strategies
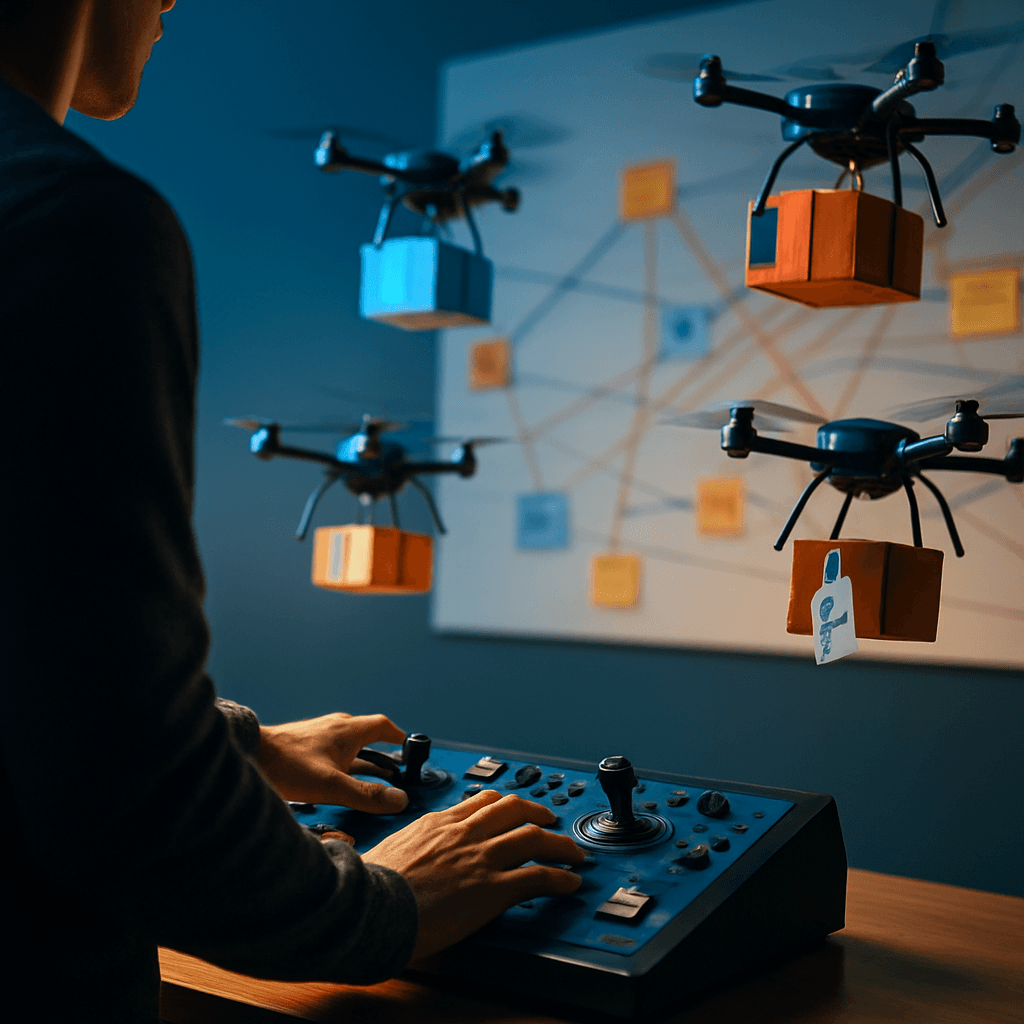
To guard against similar exploits, website owners should implement several protective measures:
- Set up automated alerts for significant changes in search visibility
- Maintain detailed documentation of proper URL structures and formatting
- Create response protocols for handling unexpected content removal
- Build relationships with platform support teams for faster issue resolution
- Regularly audit indexed pages against expected search presence
Platform Security and Content Protection
The incident reveals broader implications for platform security and content protection. While Google’s tool aimed to improve search quality by removing outdated content, its implementation created an unintended attack vector through insufficient validation and edge case testing.
This raises important questions about how platforms can balance useful public tools with adequate security measures. It also highlights the need for more robust authentication and validation processes in content management systems.
Future-Proofing Against Search Manipulation
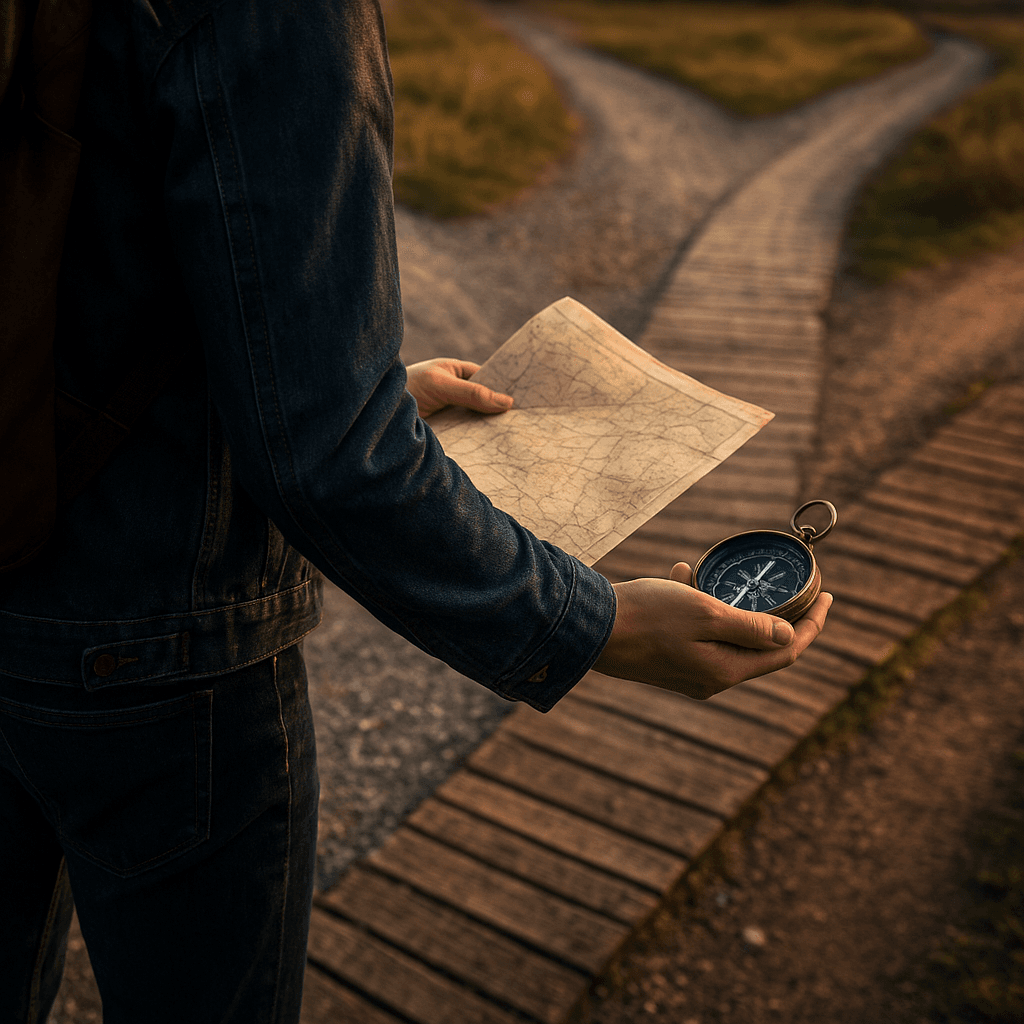
Moving forward, the vulnerability serves as a reminder that search visibility requires proactive protection. Simple technical oversights can create complex problems, especially when manipulated by determined bad actors.
The experience suggests several areas for ongoing attention:
- Regular security audits of content management processes
- Implementation of strong URL handling practices
- Development of comprehensive monitoring systems
- Creation of rapid response plans for visibility issues
As search engines continue evolving and new tools emerge, what other seemingly minor technical details might create unexpected vulnerabilities in our content visibility systems?